Almost 52,000 internet-exposed Tinyproxy cases are weak to CVE-2023-49606, a just lately disclosed crucial distant code execution (RCE) flaw.
Tinyproxy is an open-source HTTP and HTTPS proxy server designed to be quick, small, and light-weight. It’s particularly tailor-made for UNIX-like working methods and is usually used by small companies, public WiFi suppliers, and residential customers.
Firstly of the month, Cisco Talos disclosed CVE-2023-49606, a crucial (CVSS v3: 9.8) use-after-free flaw the researchers found in December 2023, impacting variations 1.11.1 (newest) and 1.10.0, after claiming to not receiving a response from the builders.
Cisco’s report shared detailed details about the vulnerability, together with proof-of-concept exploits that crashed the server and will probably result in distant code execution.
Talos researchers defined within the report that the flaw happens within the ‘remove_connection_headers()’ perform, the place particular HTTP headers (Connection and Proxy-Connection) are usually not appropriately managed, resulting in reminiscence being freed after which incorrectly accessed once more.
This may be simply exploited with a easy malformed HTTP request (e.g., Connection: Connection) with out requiring authentication.
Cisco warned on the time that regardless of its efforts to alert Tinyproxy’s builders of the crucial flaw, it acquired no response, and no patch was accessible for customers to obtain.
On Saturday, Censys reported seeing 90,000 internet-exposed Tinyproxy providers on-line, of which about 57% had been weak to CVE-2023-49606.
Particularly, Censys discovered 18,372 cases operating the weak model 1.11.1 and one other 1,390 operating on 1.10.0.
Most of those cases are situated in the US (11,946), adopted by South Korea (3,732), China (675), France (300), and Germany (150).
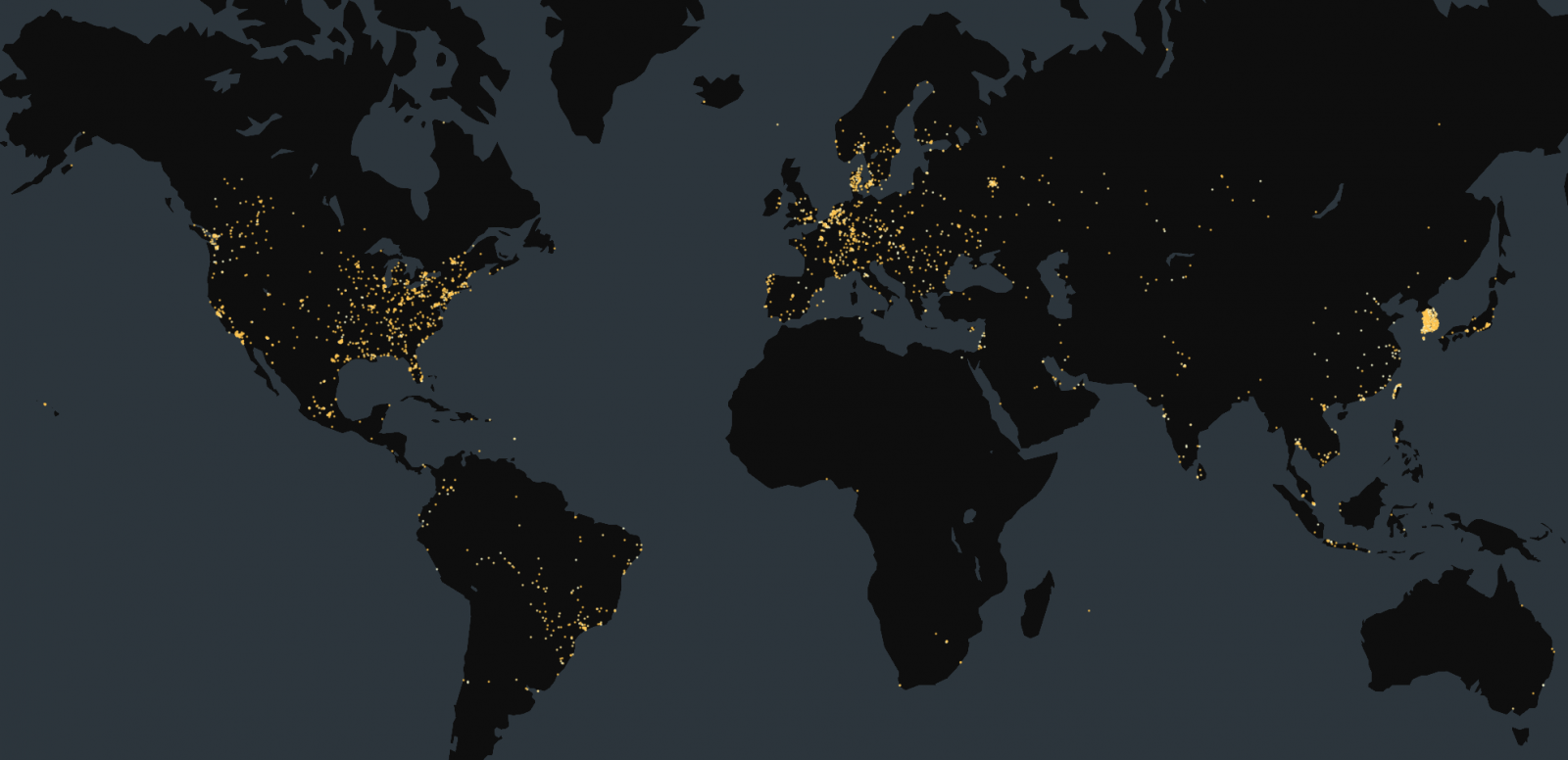
Supply: Censys
Flaw mounted
On Sunday, 5 days after Cisco disclosed the bug, the maintainers of Tinyproxy launched a repair for CVE-2023-49606, which adjusts reminiscence administration as wanted to stop exploitation.
Nevertheless, the Tinyproxy maintainer disputed that Cisco correctly disclosed the bug, stating they by no means acquired the report by way of the venture’s requested disclosure channels.
“A safety researcher from TALOS intelligence discovered a use-after-free vulnerability in tinyproxy in december 2023, claiming to have contacted upstream and waited 6 months for publication,” famous the builders on GitHub
“No matter he did to contact upstream, it wasn’t efficient and never what was described on both the tinyproxy homepage nor in README.md.”
“He actually did not attempt exhausting to discover a responsive contact, and doubtless pulled a random electronic mail handle out of git log and despatched a mail there. The vulnerability was made public on could 01 2024, and it took a full 5 days till i used to be notified on IRC by a distro package deal maintainer.”
The commit (12a8484) containing the safety repair is within the upcoming model 1.11.2, however individuals in pressing want can pull the change from the grasp department or manually apply the highlighted repair.
“It is a fairly nasty bug, and will probably result in RCE – although i have never seen a working exploit but,” continued the Tinyproxy maintainers.
“What it actually permits is a DOS assault on the server if tinyproxy is both utilizing musl libc 1.2+ – whose hardened reminiscence allocator mechanically detects UAF, or constructed with an handle sanitizer.”
The builders additionally famous that the up to date code solely triggers after passing authentication and entry record checks, which means the vulnerability may not have an effect on all setups, particularly these inside managed environments like company networks or these utilizing fundamental authentication with safe passwords.
