
Comply with this real-life community assault simulation, masking 6 steps from Preliminary Entry to Knowledge Exfiltration. See how attackers stay undetected with the best instruments and why you want a number of choke factors in your protection technique.
Surprisingly, most community assaults are usually not exceptionally refined, technologically superior, or reliant on zero-day instruments that exploit edge-case vulnerabilities. As an alternative, they typically use generally out there instruments and exploit a number of vulnerability factors. By simulating a real-world community assault, safety groups can check their detection techniques, guarantee they’ve a number of choke factors in place, and show the worth of networking safety to management.
On this article, we show a real-life assault that would simply happen in lots of techniques. The assault simulation was developed based mostly on the MITRE ATT&CK framework, Atomic Pink Workforce, Cato Networks’ expertise within the subject, and public risk intel. In the long run, we clarify why a holistic safety strategy is vital for community safety.
The Significance of Simulating a Actual-life Community Assault
There are three benefits to simulating an actual assault in your community:
- You’ll be able to check your detections and ensure they determine and thwart assaults. That is necessary for coping with run-of-the-mill assaults, that are the most typical kinds of assaults.
- Actual assaults assist you to show that protection depends on a number of choke factors. An assault is nearly by no means the results of a single level of failure, and due to this fact, a single detection mechanism is not sufficient.
- Actual assaults assist you to show the significance of community monitoring to your management. They present how actual visibility into the community offers insights into breaches, permitting for efficient mitigation, remediation, and incident response.
The Assault Stream
The assault stream demonstrated beneath relies on six steps:
- Preliminary Entry
- Ingress Device Switch
- Discovery
- Credential Dumping
- Lateral Motion and Persistence
- Knowledge Exfiltration
These steps have been chosen since they exemplify widespread strategies which can be ubiquitous in assaults.
Now, let’s dive into every step.
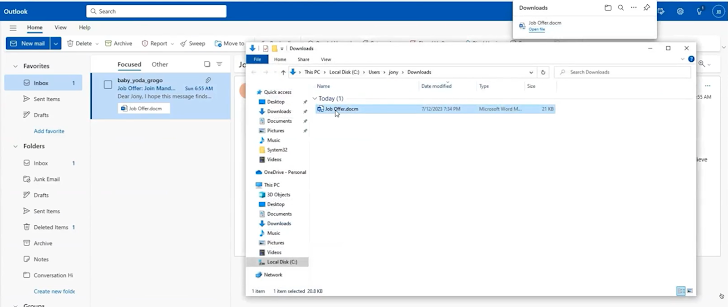
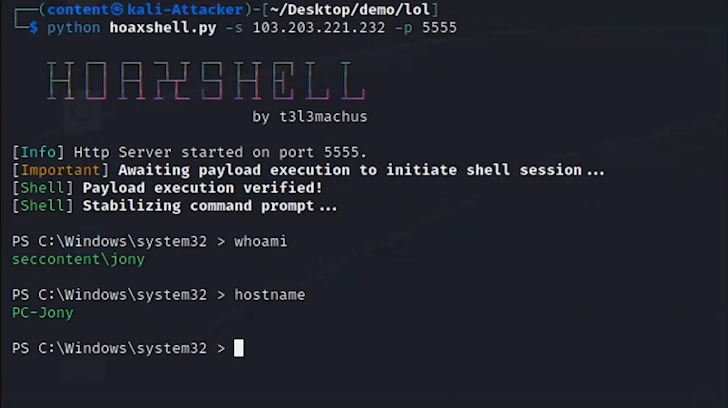
1. Preliminary Entry
The assault begins with spear-phishing, which establishes preliminary entry into the community. For instance, with an electronic mail despatched to an worker with a profitable job supply. The e-mail has an connected file. Within the backend, the malicious attachment within the electronic mail runs a macro and exploits a distant code execution vulnerability in Microsoft Workplace with a Hoaxshell, which is an open-source reverse shell.
Based on Dolev Attiya, Workers Safety Engineer for Threats at Cato Networks, “A defense-in-depth technique may have been helpful as early as this preliminary entry vector. The phishing electronic mail and the Hoaxsheel may have been caught by way of an antivirus engine scanning the e-mail gateway, an antivirus on the endpoint or by way of visibility into the community and catching command and management of the community artifact generated by the malicious doc. A number of controls improve the prospect of catching the assault.”
2. Ingress Device Switch

As soon as entry is gained, the attacker transfers varied instruments into the system to help with additional levels of the assault. This contains Powershell, Mimikatz, PSX, WMI, and extra instruments that stay off the land.
Attiya provides, “Many of those instruments are already contained in the Microsoft Home windows framework. Normally, they’re utilized by admins to regulate the system, however attackers can use them as nicely for comparable, albeit malicious, functions.”
3. Discovery
Now, the attacker explores the community to determine invaluable sources, like companies, techniques, workstations, area controllers, ports, further credentials, energetic IPs, and extra.
Based on Attiya, “Consider this step as if the attacker is a vacationer visiting a big metropolis for the primary time. They’re asking individuals find out how to get to locations, trying up buildings, checking road indicators, and studying to orient themselves. That is what the attacker is doing.”

4. Credential Dumping
As soon as invaluable sources are recognized the beforehand added instruments are used to extract credentials for a number of customers to compromised techniques. This helps the attacker put together for lateral motion.
5. Lateral Motion and Persistence
With the credentials, the attacker strikes laterally throughout the community, accessing different techniques. The attacker’s aim is to develop their foothold by attending to as many customers and units as doable and with as excessive privileges as doable. This permits them to hunt for delicate information they will exfiltrate. If the attacker obtains the administrator’s credentials, for instance, they will acquire entry to giant components of the community. In lots of instances, the attacker would possibly proceed slowly and schedule duties for a later time period to keep away from being detected. This enables attackers to advance within the community for months with out inflicting suspicion and being recognized.

Etay Maor, Sr. Director of Safety Technique, says “I am unable to emphasize sufficient how widespread Mimikatz is. It is extraordinarily efficient for extracting passwords, and breaking them is simple and may take mere seconds. Everybody makes use of Mimikatz, even nation-state actors.”
6. Knowledge Exfiltration
Lastly, invaluable knowledge is recognized. It may be extracted from the community to a file-sharing system within the cloud, encrypted for ransomware, and extra.
Learn how to Shield In opposition to Community Assaults
Successfully defending in opposition to attackers requires a number of layers of detection. Every layer of safety within the kill chain should be strategically managed and holistically orchestrated to stop attackers from efficiently executing their plans. This strategy helps anticipate each doable transfer of an attacker for a stronger safety posture.
To observe this complete assault and be taught extra a couple of defense-in-depth technique, watch the complete masterclass right here.
