
A brand new ongoing malware marketing campaign has been noticed distributing three totally different stealers, reminiscent of CryptBot, LummaC2, and Rhadamanthys hosted on Content material Supply Community (CDN) cache domains since not less than February 2024.
Cisco Talos has attributed the exercise with average confidence to a menace actor tracked as CoralRaider, a suspected Vietnamese-origin group that got here to gentle earlier this month.
This evaluation is predicated on “a number of overlaps in ways, methods, and procedures (TTPs) of CoralRaider’s Rotbot marketing campaign, together with the preliminary assault vector of the Home windows Shortcut file, intermediate PowerShell decryptor and payload obtain scripts, the FoDHelper approach used to bypass Consumer Entry Controls (UAC) of the sufferer machine,” the corporate mentioned.

Targets of the marketing campaign span numerous enterprise verticals throughout geographies, together with the U.S., Nigeria, Pakistan, Ecuador, Germany, Egypt, the U.Ok., Poland, the Philippines, Norway, Japan, Syria, and Turkey.
Assault chains contain customers downloading recordsdata masquerading as film recordsdata by way of an internet browser, elevating the opportunity of a large-scale assault.
“This menace actor is utilizing a Content material Supply Community (CDN) cache to retailer the malicious recordsdata on their community edge host on this marketing campaign, avoiding request delay,” Talos researchers Joey Chen, Chetan Raghuprasad, and Alex Karkins mentioned. “The actor is utilizing the CDN cache as a obtain server to deceive community defenders.”
The preliminary entry vector for the drive-by downloads is suspected to be phishing emails, utilizing them as a conduit to propagate booby-trapped hyperlinks pointing to ZIP archives containing a Home windows shortcut (LNK) file.
The shortcut file, in flip, runs a PowerShell script to fetch a next-stage HTML utility (HTA) payload hosted on the CDN cache, which subsequently runs Javascript code to launch an embedded PowerShell loader that takes steps to fly below the radar and finally downloads and runs one of many three stealer malware.

The modular PowerShell loader script is designed to bypass the Consumer Entry Controls (UAC) within the sufferer’s machine utilizing a identified approach referred to as FodHelper, which has additionally been put to make use of by Vietnamese menace actors linked to a different stealer often called NodeStealer that is able to stealing Fb account knowledge.
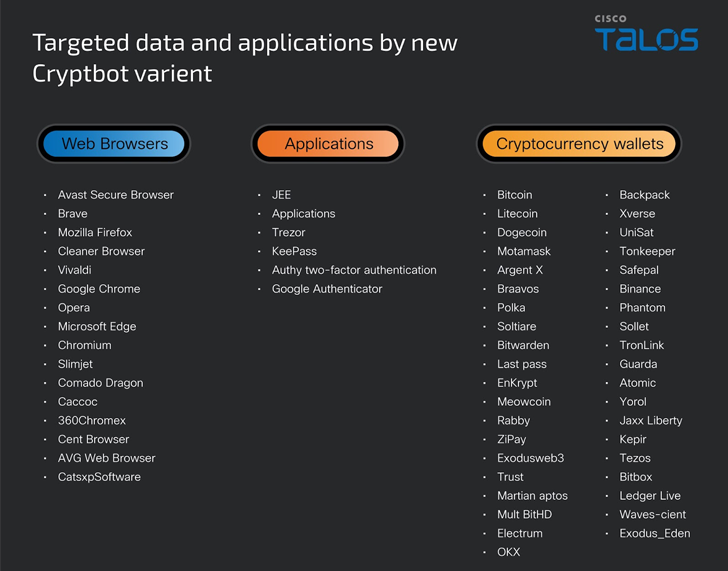
The stealer malware, no matter what’s deployed, grabs victims’ info, reminiscent of system and browser knowledge, credentials, cryptocurrency wallets, and monetary info.
What’s notable concerning the marketing campaign is that it makes use of an up to date model of CryptBot that packs in new anti-analysis methods and in addition captures password supervisor utility databases and authenticator utility info.
